About me
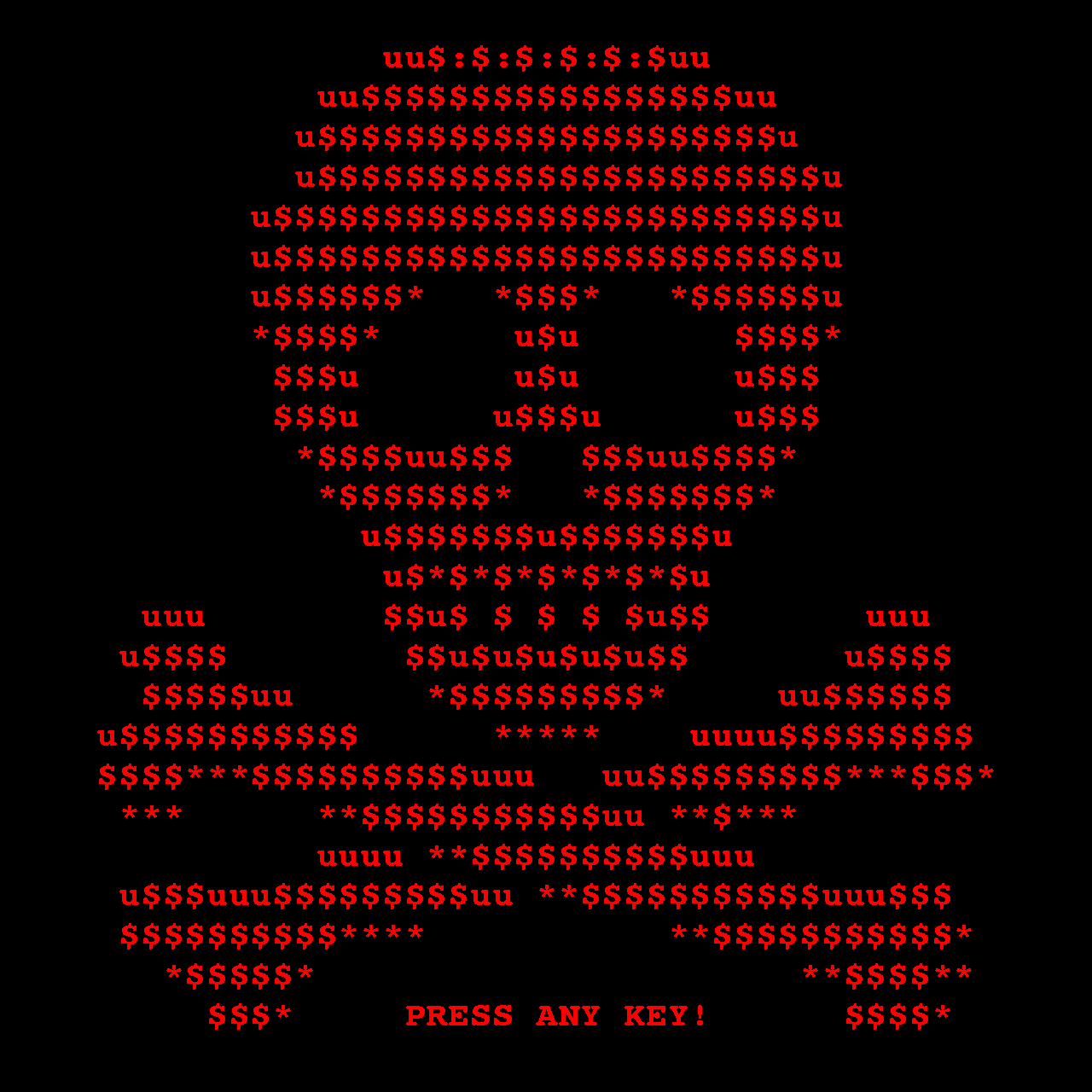
Information Technology + Cybersecurity
As a young child, I have always been intrigued by technology. I would always tinker around playing with components and trying to figure out how things worked. As I grew throughout the years, I followed those interests, expanding my ever-growing education. With that, let me show you what I can do.
Download Resume